What Is Encryption and How Does It Work?
Computers, mobile devices and instant connections to the internet are seemingly everywhere. With that instant connectivity comes the rapidly increasing threat of cybercrime and other intrusions on your privacy.
The internet presented a new, profitable frontier for cyber criminals, which makes protecting your online privacy more important than ever.
One of the best ways to protect your privacy and valuable personal data on the internet? Encryption.
While you may not be aware of this, encryption already protects many of your daily online activities. Online banking, email, online shopping – even the website you’re currently visiting – all use encryption to protect your data.
Encryption isn’t a recent creation. Thousands of years ago, Greeks and Egyptians used cryptography (a form of encryption) to keep important messages safe from prying eyes.
Rest assured, today’s encryption uses techniques and methods that are much more powerful and secure than the ancient users’ simple character-replacement algorithms.
Before we take a look at how modern encryption works, let’s take a quick look at the history of encryption.
History of Encryption
Encryption has been in use since well before most people could read or write. The first documented instance of written cryptography dates back to 1900 B.C., when an Egyptian scribe used non-standard hieroglyphs in an inscription.
The word encryption comes from “kryptos.” The Greeks used “krypto” to describe something that was hidden or secret.
In 700 B.C., the Spartans wrote important messages on leather, which was wrapped around sticks. A message could only be read by someone who had a stick of the exact same diameter. Without knowing the exact diameter size, a person wouldn’t be able to decipher the message (which means to convert the code into understandable text).
Later, Hebrew scribes developed an encryption model called “ATBASH.” This type of encryption used a reversed-alphabet simple substitution code. That means that an “A” becomes a “Z,” “B” becomes a “Y,” etc.
For example, “Hello” would be encoded as “Svool.”
In the time of Julius Caesar (100-44 B.C.), the Romans used a similar substitution, known today as the “Caesar Shift Cipher.” Instead of reversing the alphabet, the Romans used a pre-agreed shift of the letters – only the person who knew about the agreed shift of letters could decipher the message.
For example, if the agreed shift was 5, then the sentence “This is super interesting!” would be encrypted into “YMNX NX XZUJW NSYJWJXYNSL!”
The Middle Ages brought a rapid development of encryption types that used polyalphabetic substitution (multiple substitution alphabets used to minimize the success of decryption).
Perhaps the most important development in modern encryption took place in the period of 1933 to 1945, when German cryptologists created and continually improved the world-famous Enigma machine. Until this development, all encryption models were designed using a symmetric key – I’ll discuss the Enigma machine later on.
In the mid-1970s, IBM created an encryption model that was adapted as the U.S. Data Encryption Standard (DES). Some observers feared that DES included a backdoor that could be used by the U.S. National Security Agency (NSA) to decipher messages encrypted using the standard. It was later replaced by AES encryption, which I’ll discuss later.
In 1976, Whitfield Diffie and Martin Hellman published “New Directions in Cryptography,” which laid the groundwork to solve one of the core fundamental issues (at the time) of encryption schemes: how to distribute the encryption key to the intended person(s) in a safe and secure way.
New Directions in Cryptography was considered a breakthrough and triggered an era of new cryptography schemes, using a public key with asymmetric algorithms and new authentication methods – which I will explain in depth in the “asymmetric” section of “Types of Key Algorithms.”
What Is Encryption?
Encryption is a modern, electronic version of ancient cryptography schemes. Modern encryption is based on complex algorithms called “ciphers.”
Encryption is designed to protect important information from prying eyes by turning plaintext (readable-to-humans) data into a string of ciphertext, which is impossible to read without the proper decryption key.
The best example of plaintext is what you are reading now. The text you are currently reading is plaintext, as you can read it.
Ciphertext is encrypted information that contains the original plaintext information, but is stored in a way that humans can’t read, and even computers can’t if they lack the proper decryption key.
Encryption keys are designed to be a one-off, unique algorithm used to encode and decode data. By using an encryption key, you can encrypt data and send it to a friend, who can use the same key (which you supply) to decrypt the information, turning it into readable data.
The above process is known as symmetric encryption, which uses a single unique key to both encrypt and decrypt information. (Asymmetric encryption, which I’ll discuss a bit later, works differently.)
Machine cryptography – or rotor machine – became known to the majority of the public during WWII, when the Germans used the Enigma code (machine) to encrypt all of their communications.
Machine cryptography consists of an electro-mechanical system which is used to encrypt and decrypt secret information.
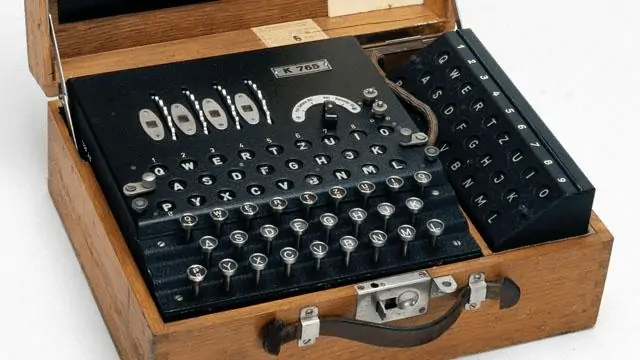
The German government encrypted all of their communication channels, from attack coordination and strategy planning to reporting. It became one of Great Britain’s most important and secret tasks to decrypt the Enigma machine in order to know what the Nazis were planning to do.
British mathematician Alan Turing – along with others in a group of Britain’s greatest mathematicians – set out to decrypt the Enigma code in a then-secret location at Bletchley Park in England.
Turing and Gordon Welchman managed to build the code-breaking machine dubbed “Colossus.” The vacuum tube-powered machines became the first programmable digital computer that could generate unique and strong encryption and decryption keys, which was a massive turning point in both WWII and the development of encryption and decryption.
1) What Is the Encryption Algorithm Used For?
Although encryption was mainly used by governments and large corporations before the 1970s, the groundbreaking introduction of Whitfield Diffie and Martin Hellman’s “New Directions in Cryptography” changed that in 1976.
Their work led to the introduction of the RSA algorithm on personal computers. Eventually, encryption became widely implemented in web browsers and data servers to protect data.
In today’s world, encryption is universally used to protect data in e-commerce, online payment and banking, email software, cryptocurrency, customer data storage and much more. The data that is stored on your iPhone or Android device is also encrypted. (Which frustrates police and other government agencies to no end.)
Additionally, SIM cards, top-up boxes and properly-set-up Wi-Fi networks all employ encryption algorithm protocols to encrypt and protect their users’ sensitive data.
Encryption also protects data that’s being communicated between two parties – for example, the credit card details of a customer when they’re making an online purchase.
While the data can still be intercepted, it would be unintelligible and therefore useless to spies or hackers.
All sorts of devices across a wide variety of different networks encrypt communication in transit. Encryption is not only used for internet transits, but also ATM transactions or mobile phone calls.
Encryption algorithms protect all data in transit.
2) Examples of a Primitive Encrypted Message
As mentioned previously, there are simple encryption schemes and then there are highly-advanced ciphers.
Remember the ATBASH or Roman encryption scheme? An example of that would look like the following. You may remember using a similar code to pass “secret” messages back and forth back in grade school.
As you can see in the image above, I selected “Key:2,” which means that “A” will be “C,” “B” will be “D,” and so forth.
If I change the settings, I can also include numbers. If I change the “Key” value, it increases in complexity.
If you want to try it out yourself, visit the Crypto Corner website.
3) Example of a Modern Encrypted Message
While we haven’t as yet taken a look at the concepts of modern-day encryption methods, I wanted to include the example below to give you an idea of what I’ll be talking about later.
Let’s take a look at a very advanced form of encryption. This is an example of current encryption methods, which will be fully explained in the “Types of Key Algorithms” section.
For this example, I’ll use the “Pretty Good Privacy” (PGP) encryption program.
So, imagine you used an email provider with encryption security protection. Generally, an email would only show plaintext, but if you don’t have the decryption key to an encrypted email, it could look like the following.
Step #1: Create a private and public key.
Step #2: Click on “Generate PGP Keys.”
The result could be something like the image below.
Step #3: Visit the encryption page.
For full effect, here’s a copy of the final sequence of ciphertext (encrypted email):
hQEMAzfgieoHtIH5AQf/YVNmilR2WcFy26XyQElKi8fFcaA3GvM2RwC+u7tvKBB+PqUGW1sNE1t4t9FP+I42YrA/FhWle1Iw4QeB/f6SPBsvHWIX7kcWcC3fymqfTUjH5kXoUfOZtbOVYEjrVNVoffG0J9BI3MoAe9DprwyTDeUbBUJGN7ftRnoMJZD2TWfBk4E/Qdfto5jPkB3UxHDQQAukWOCGVhEdz8EhnogL04YHmEUhFttCbGoL4lfCQ8liCBclkLTgDvkcWrq4CsQ+VzCrWESoIptaTDptV0
2owZ7C+q6aAlGKVaZmeFUH4izv/Q0C3CncGT2BSvNDw+sPbpsuv1JQ18Qolx1VnuoYcnAHbHtwlIBnZOn4/h/Nhp3pjROcGx11dqreMI9uOIpoI7WaA9we92kgd782MggGVWrs0G2idxJYwIBVx42yOQiRKumH/S/OxolFavk5ewoaro/MqUFZHERx2PDM38sX03G3aDK6VyoBhWTHDUvBzt5oPLDxFOvM7foDFS6MBga/2frrk+V/ud9CrNXa82l5GCzjY3gZ6q8n901iuUmqT3e5pJF5XgeIdxhIxOynRa6Mk9YzWWmCpZ27rmpm2hF11vG7z22vRt8EoBVPvn+9nptYO5N+f+3E1WjWItaUBme=LTfL
As you can see, the plaintext email message that I wrote changed into a piece of unintelligible text. This text is unreadable and is useless to anyone who intercepts my email message (for those who don’t have the public encryption key).
If you want to test it out yourself, visit the iGolder website (click on “PGP Key Generator” first).
4) What Does “Encryption Algorithm” Mean?
In its most basic form, the encryption program runs a formula to turn your data (plaintext) into ciphertext – secret and unreadable data.
This process works inversely as well. So, ciphertext can be reverted into plaintext (which you can read).
In the first example in the previous section, there was only one calculation carried out, which moved each letter of the alphabet forward by 2.
The second encryption example shown has a much higher number of bits, which means there’s an incredible number of potential calculation patterns.
By transforming data or plaintext into ciphertext, the prying eyes of hackers or other nosy Nellies will be unable to read the information.
Every single encryption algorithm makes use of a string of bits – widely known as the “key” – to execute the calculations. The longer the encryption key (the more bits), the more possible calculation patterns can be created, and the harder it will be to decrypt the ciphertext without a key.
The majority of the encryption algorithms use the “block cipher method.” This method applies a random algorithm in combination with a symmetric key to encrypt a block of text.
This method encrypts the fixed blocks of input, which generally range from 64 to 128 or 256 bits in length.
A less popular and occasionally-used method is the “stream method.” This method applies to plaintext digits that are combined with a pseudorandom cipher digit stream – or “keystream.” The algorithm applies to each binary digit in a data stream, one bit per input.
How Does the Encryption Work & What Is the Role of the Key?
The encryption/decryption key is comparable with a normal password – the one you use for your email, for example. The key is an essential part of the process of encoding and decoding data.
Typically, a key is a random binary or an actual passphrase. The key “tells” the algorithm what patterns it must follow in order to convert plaintext into ciphertext (and the other way around).
It almost goes without saying, but the key is a fundamental part of the protection of the privacy of information, a message or a piece of data. The encryption and decryption process can only be initiated by using the key.
Due to the fact that algorithms are publicly available and can be accessed by anyone, once a hacker gets a hold of the encryption key, the encrypted data can easily be decrypted to plaintext.
The hacker can either crack the random binary or passphrase of the key, or the hacker could hack into your system and obtain the key by stealing it from you.
Therefore, it’s incredibly important to create a very strong combination of different letters (lowercase and uppercase), numbers and special characters. Or, even better, regularly change the combination of the key.Usually, a larger key size (longer key) means that the complexity is greater. So, the security is better.
When you create a new key size for a specific set of data, it’s best to use a virtual keyboard when entering the letters, numbers and special characters.
A virtual keyboard protects you against potentially-installed keyloggers (malware) in your system, which register everything you do on your PC. By using a virtual keyboard, you’re not actually using your tangible keyboard, but instead, you’re clicking on a secondary keyboard on your screen (which can’t be logged by a keylogger because it’s all visual).
Furthermore, digital encryption is highly complex and considered to be significantly difficult to crack.
In order to add another layer of complexity (and security) to smartphone encryption, every time a pair of smartphones establishes a communication channel, an additional shell of protection is built around that channel. The shell is basically a new set of algorithms establishing a secure connection.
Many security- and privacy-focused email providers and chat services protect the data of their users by implementing end-to-end encryption. Similar to the other types of encryption, it mixes up the messages into ciphertext.
While other encryption methods work in pairs – one key encrypts the data, while the other key can be used and distributed to other parties to decrypt the data – end-to-end encryption works differently.
End-to-end encryption basically means that only the one who sends the message and the one who receives it can read it.
For example, chat services such as Telegram and WhatsApp end-to-end encrypt every message that the user sends. The software is developed in such a way that every plaintext message is converted into ciphertext and can only be decrypted – viewed in plaintext – by the recipient.
Simply put, when you send an email using end-to-end encryption security, not even the email service provider can read your message because it’s already encrypted on their server.
1) Types of Key Algorithms
A fundamental pillar to establish a secure communication is based on the significance of the key.
There are two methods of encryption:
- Symmetric Key Algorithms: Symmetric algorithms use similar or exactly the same encryption keys for both the encryption of plaintext and the decryption of ciphertext.
- Asymmetric Key Algorithms: Asymmetric algorithms use different (unique) keys for the encryption of plaintext and the decryption of ciphertext.
The asymmetric algorithm method is often referred to as “public-key cryptography.”
While I touched on this briefly earlier in the article, a more detailed description is provided below.
Symmetric Key Algorithms
Symmetric algorithms use the exact same key for encrypting plaintext and decrypting ciphertext. Symmetric key algorithms are often established like the following example:
When two parties want to communicate certain data or information in a secure and secret manner, the two parties can exchange the passphrase of the key before sharing the data. This could, for example, be done over the phone or in a face-to-face meeting.
Then, the two parties agree that a specific key (password) will be used to secure all the information and messages exchanged in the future.
This type of encryption is easy to use for all parties involved because they only need to exchange the encryption and decryption key once. From then onward, all communication between the two parties is secure.
In contrast, asymmetric algorithms require a new key for every new instance of communication between two parties.
Additionally, symmetric key algorithms are faster than asymmetric ones because there’s only one key. Asymmetric algorithms use a pair of keys that are mathematically connected – increasing the mathematical complexity.
A major disadvantage of symmetric key algorithms is that if someone who’s not authorized to view the data or information is able to obtain the key, that person can easily decrypt the intercepted message that was sent between the two parties.
If you have a lot of different communication channels with different parties, it can be challenging to manage every unique key that belongs to a certain person you’re in communication with.
Asymmetric Key Algorithms
In contrast to the single key symmetric algorithms, asymmetric key algorithms use a pair of two keys in order to execute the algorithm.
One key is used for the encryption of plaintext and the other key is used for the decryption of ciphertext.
The two keys are a combination of letters, numbers and special characters that create randomly-generated strings.
The asymmetric encryption key uses a private key and a public key. That means that the one sending a message can encrypt it with a private key that was not shared with the receiving party. Instead, the public key is available for anyone to use – however, it only provides access to a limited piece of information.
Let’s explore that further.
Asymmetric encryption establishes an authentication. During the authentication process, the function of the public key is to verify that the message is sent by the private key pair holder. In return, only the paired private key holder can decrypt the message encrypted with the public paired key.
For example, imagine that the email conversations between my friends and I are encrypted. But, unfortunately, my friend is careless with their key and a hacker obtains their private key.
If that hacker was able to intercept all my email data, he would now be able to read the messages between my careless friend and me. But, the compromised private key would not provide access to any other messages I’ve sent.
The essential advantage here is that my other data would be safe and secure because the other people I’ve sent messages to provided me with different keys.
The private key is created based on highly complex mathematical calculations, which is linked to the public key pair. Simply put, if a message or set of data is encrypted with a public key, only its private key pair can decrypt it – and vice versa.
The biggest advantage of using asymmetric key algorithms is that you never need to share or send your encryption key or passphrase over an insecure channel. So, that drastically reduces the possibility of getting hacked.
The public key can be shared with anyone without compromising security, since any person can encrypt a message using the receiver’s public key. But, the encrypted message can only be decrypted to plaintext by the private key holder.
Asymmetric key algorithms have three disadvantages:
- You need to complete the authentication process with a public key every time a message is sent.
- If you lose the private key, it’s impossible to decrypt the ciphertext.
- Processing the asymmetric algorithm is much slower compared to the symmetric algorithm due to its mathematical complexity, and it’s therefore not suitable to compute vast amounts of data.
2) How Does Encryption Secure Online Communication?
The Secure Sockets Layer (SSL) protocol is an encryption method that creates a secure connection between a web server and your browser.
That means that the data you’re transmitting to the web server is protected from unwanted snoops. You can recognize a secure web server by checking for the following in your search bar:
This is how the process works:
The web server provides your web browser its certificate with its public key. Then, the browser checks whether the certificate was issued by a Certificate Authority (a trusted provider of SSL protection).
Your browser then uses this public key to encrypt the data you are sending to the web server.
In order to read the encrypted data, the web server uses its private key to decrypt the ciphertext.
In other words, only the web server is able to read your data, because only the web server has the private key to decrypt your data. This process makes sure that your data is protected from hackers.
Advanced Encryption Standard (AES)
The Advanced Encryption Standard is a symmetric block cipher and a subset of the Rijndael cipher.
The U.S. National Institute of Standards and Technology chose this method of symmetric encryption as the top security encryption standard. The U.S. government therefore adopted the AES, which is now used on a worldwide scale to protect classified information and encrypt sensitive data in software and hardware.
1) How Does AES Encryption Work?
The AES uses three different block ciphers:
- AES-128
- AES-192
- AES-256
Every individual block cipher is able to encrypt and decrypt data in a fixed block size of 128-bits. The key size is 128, 192 or 256 bits respectively.
The difference between the Rijndael cipher and the AES cipher is that the Rijndael cipher accepted additional block and key sizes, but the AES cipher did not implement those functions.
2) What Is the Meaning of Block Size?
Every algorithm processes block ciphers in a particular size.
In other words, the algorithm “breaks” the data or plaintext into blocks and processes the calculations block by block.
Every block contains a fixed size of bits: for example (as shown above), 128, 192 or 256 bits. The complete string of input text will be split into the exact same-sized blocks while the algorithm is processing the encryption or decryption of the data.
Each block of plaintext has a corresponding block of ciphertext for a specific key (and vice versa).
3) What Is the Meaning of Key Size?
The key size stands for the number of bits in the key. For the AES, the key size is directly linked to the strength of the algorithm. The higher the number of bits, the stronger its security.
So, 256-bits provides extra security in comparison to 128-bits.
Short keys can be vulnerable to brute force attacks. That being said, AES encryption is nearly impossible to crack with brute force.
Let’s look at an interesting example calculation taken from Seagate’s Technology paper “128-Bit Versus 256-Bit AES Encryption.”
To put it into perspective, if:
- Every person on the planet owned 10 computers
- There are 7 billion people on earth
- Each of the computers can test 1 billion key combinations per second
- On average, you can crack the key after testing 50% of the possibilities
Then, given those conditions, the earth’s population could crack one encryption key in 77,000,000,000,000,000,000,000,000 years! And that’s only for 128-bit AES encryption!
Weaknesses in Encryption
Especially after seeing the calculation shown above, you might believe that encryption algorithms are absolutely unbreakable.
Unfortunately, that’s not true.
As new weaknesses are exploited, new encryption methods are created to counter these exploits in order to build new layers of security.
The biggest weakness of encryption algorithms is the fact that some algorithms fail to generate seemingly random strings of ciphertext, but instead generate recognizable patterns. When a hacker is able to identify a pattern, it aids them greatly in cracking the ciphertext.
This issue also applies to algorithms that generate patterns that are predictable, as a result of repetitive data input tests.
It’s unlikely for a hacker to crack all cipher blocks, but exposing only a few blocks could already lead to the leakage of crucial, sensitive data – with possibly disastrous consequences.
However, the time, effort and computational cost that are needed to crack an algorithm such as the AES makes it an extremely expensive endeavor, and an attempt is rather pointless.
The biggest threats to the security of encrypted data are mostly outside the power of technology. Think about keyloggers that log what key or passphrase you enter, as well as backdoors and other forms of malware that are used to obtain encryption keys.
If you want to protect your Windows or Mac device against such threats, read my post on the best antivirus software.
What Have We Learned? (Don’t Be Overwhelmed!)
Awesome! You’ve made it to the very end of this extensive, information-packed guide to give you a better understanding of what encryption is and how it works.
It’s safe to say that data protection is important to everyone, not just to governments and large enterprises. Your own privacy is on the line!
Now you know that encryption transforms plaintext (readable text) into ciphertext (unreadable text).
Generally, encryption works like that, but there are different methods such as symmetric and asymmetric encryption, which both take a different approach on how the data is encrypted and how it can be decrypted.
Now it’s time to enjoy a safe way of sending and receiving sensitive data and messages!